Professional Crypto Laundering
An Assessment of the Figueira Indictment – Methodology, Red Flags & Actions To Take
📅 March 18, 2026
📅 March 18, 2026
In January 2026, the U.S. Department of Justice indicted* Venezuelan national Jorge Figueira for laundering almost $1 billion using a highly advanced methodology that included cash, crypto, Over-the-Counter (OTC) brokerages registered in the UK and United States, and shell companies with accounts at regulated financial institutions.
“Do you know who has excellent technology tools to do money laundering? The Chinese. But we do too. I spent money on monitoring, and I have supervision and control tools…” – Jorge Figueira recorded in an FBI audio recording, translated from Spanish
While Chinese Money Laundering Networks (CMLNs) have attracted significant attention – representing $312 billion in suspicious activity reports filed with FinCEN over 2020-2024 – other professional money launderers are also highly effective and financial institutions must ensure they are taking action on these networks and their typologies too.
According to the indictment^, Figueira and his transnational network could also launder at immense and multi-national scale:
* A criminal complaint is merely an accusation. The defendant is presumed innocent until proven guilty.
^ Analysis in this article is drawn from Case No. 1:25-mj-730-LRV, except where specified.
The Figueira indictment reveals the extensive capabilities and advanced knowledge of professional money launderers, making them formidable adversaries for financial institutions. In the investigation and the audio recordings made by the FBI, Figueira demonstrates an understanding of:
“That’s why I insist a lot about the screening of the wallets… The wallets can be traced. I know how to trace them. But since I know how to trace them, we know how to disguise them… [I spend] around $35,000 monthly, only on tools.”
– Jorge Figueira recorded in an FBI audio recording, translated from Spanish
Here’s how the Figueira laundering methodology worked:
Step 1: Cash deposits
Cash was deposited into bank accounts in Panama or Venezuela. This cash was the proceeds of drug trafficking or other organized criminality such as counterfeiting fashion accessories. Figueira’s network was also used to launder the proceeds of non-illicit commercial activity, where the purpose of laundering was to evade sanctions on Venezuela.
Figueira was reluctant to receive cash in the United States due to the regulatory and law enforcement attention this would attract, whereas in cash-focused economies such as Venezuela, the cash could be more easily introduced into the financial system.
Where cash was collected by Figueira’s affiliates in U.S. locations, he charged higher fees to reflect the greater risks involved. U.S. cash deposits included revenues from:
Step 2: Cash to Crypto
The cash was converted into crypto, specifically Tether (USDT) on the Tron blockchain. USDT is a stablecoin, meaning it is “pegged” to the U.S. dollar, and is less volatile in value than assets such as Bitcoin or Ethereum. USDT is also the stablecoin with the highest trading volumes of more than $100 billion every 24 hours and the highest market capitalization of more than $183 billion, which provides significant liquidity.
Transaction (“gas”) fees on the Tron blockchain are usually lower than other blockchains such as Ethereum. This is noteworthy because where crypto is going to be “layered” through multiple transactions (Step 3) in an attempt to obscure its illicit origin, each movement incurs a cost. Using blockchains with lower gas fees minimizes laundering costs.
“It [USDT] is used to transfer money in a quick way, even to make it get to jurisdictions that have some type of issues, etcetera. For example, to send it to China. It is not that easy to pay in China. Or, let’s say it because I’m from there, to bring resources from Venezuela, and to pay different accounts not only in the United States but also in other parts of Europe and Asia, through USDT, because Venezuela doesn’t have the liberty to interact with the international financial institutions because of the sanctions.” – Jorge Figueira recorded in an FBI audio recording, translated from Spanish
Step 3: Crypto Layering
The USDT was moved through multiple crypto wallets, comparable with layering fiat currency. Since each movement on the blockchain incurs gas fee costs, legitimate activity minimizes the number of movements, whereas willingness to incur these costs is indicative of illicit activity to obscure the origin of the crypto.
On average, Figueira layered crypto through 4 to 9 transactions over short periods. Examples included:
After layering, the crypto arrived in a wallet referred to by Figueira as his “macro-wallet.” The macro-wallet aggregated multiple layered flows. It received a total of 1,056,755,688.677986 USDT and sent 1,056,755,688.677986 USDT. The equivalence between the inflows and outflows are consistent with the wallet being used to “pool” crypto before onward movement.
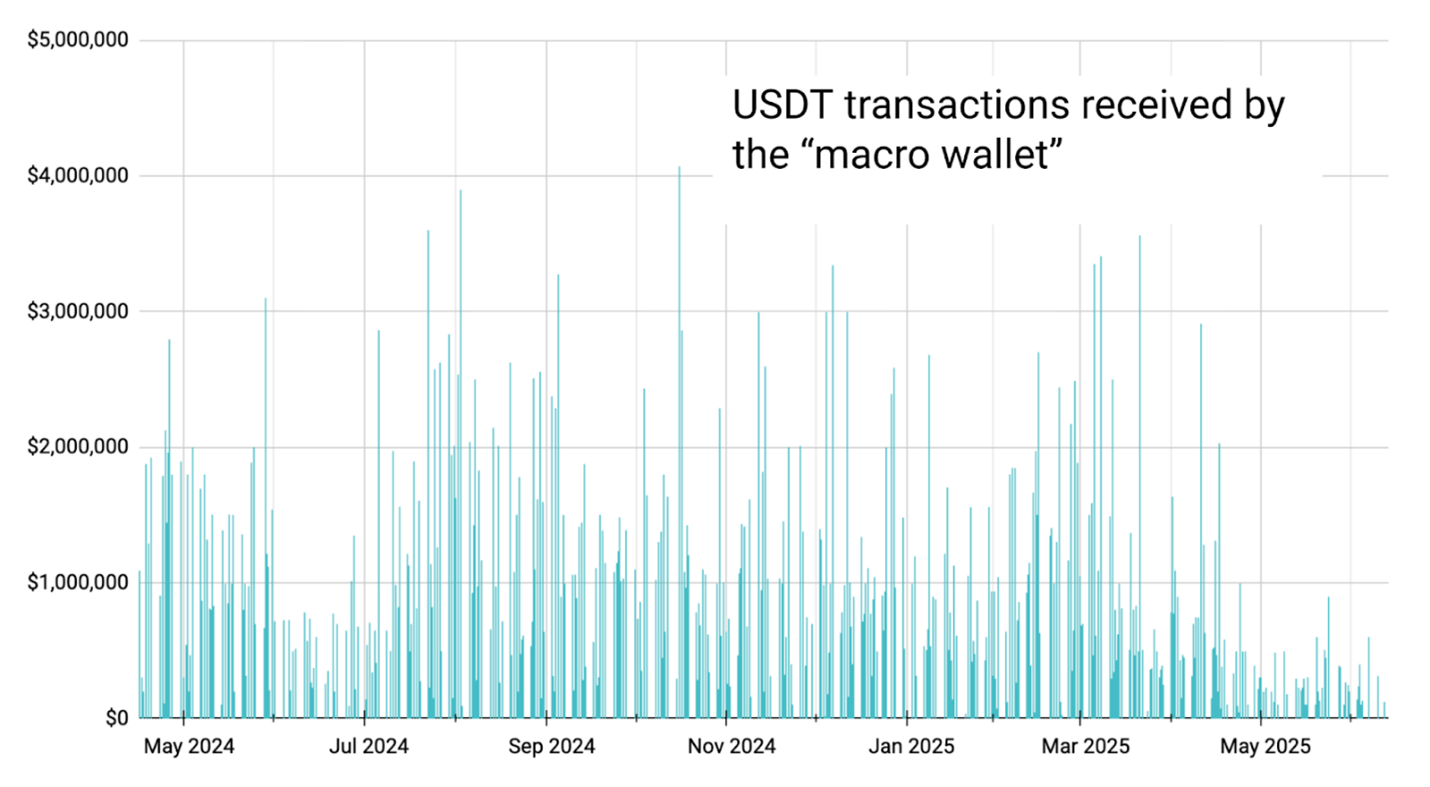
Source: Elliptic
Step 4: Offramp Using OTC Brokerages and Shell Company Bank Accounts
Figueira off-ramped the crypto back into fiat currency such as U.S. dollars using “liquidity providers” and shell companies.
The liquidity providers were OTC brokerages that facilitate trading directly between counterparties, usually to facilitate high value trades without causing the price slippage or volatility that could occur if they are traded on an exchange.
In the indictment, Figueira refers to using liquidity providers including OTC brokerages “Enigma, Anchorage, Abra” and others. Enigma, Anchorage, and Abra are regulated/registered in the United Kingdom or United States – though the indictment does not establish whether Figueira’s statements have been verified.
Figueira operated at least four shell companies to receive the conversion of crypto into fiat currency. At least one (“Company A”) was physically located in the United States, in Sunny Isles Beach, Florida.
“I can’t go and tell them [banks] that I am a money transmitter because they would close the doors for me immediately. So, I tell them that we are a credit company… that is what we do publicly, we are a credit company…” – Jorge Figueira recorded in an FBI audio recording, translated from Spanish
Figueira described how he adapted the information he presented to financial institutions that provided bank services to the shell companies to minimize detection.
“I don’t have personnel here [the business address in Florida] entering operations or entering data in the computers, receiving money, nothing… We created some webpages because it is mandatory for the banks here.” – Jorge Figueira recorded in an FBI audio recording, translated from Spanish
The FBI assessed that the companies were shell companies used for illicit purposes:
Financial institutions and crypto businesses should be alert to these red flags and should integrate them into their KYC/CDD, transaction monitoring, and investigations processes, taking appropriate action as required.
Shell Company Red Flags
🚩 Companies do not appear to have staff or operations, even if they have a website.
🚩 Transactions do not include legitimate business activity e.g. there are no payroll or business expenses.
🚩 The business is described as operating in a “finance-adjacent” sector such as trade finance consulting or credit.
Transactional Red Flags
🚩 There are indicators of pooling and/or funneling, for example the inflows are equivalent to outflows, especially where there are high value/volume/velocity flows over short periods.
🚩 Inflows and/or outflows are not consistent with the business type or involve higher risk products (such as crypto) or jurisdictions.
🚩 Crypto transactions involve multiple movements, in the absence of a business rationale.
Crypto businesses should already apply blockchain investigations and screening as part of their risk management programs, both at onboarding and throughout the client lifecycle, to identify indicators of high risk activity.
Traditional financial institutions should take action too: cases like Figueira demonstrate that professional money launderers continue to use the financial system as part of their laundering methodology, and these institutions may be a detection point into a wider laundering scheme.
These institutions should extend their financial crime compliance programs to include crypto measures – even if they do not directly service crypto clients or offer crypto products and services. In addition to red flags for shell companies or unusual transactional activity, where there are red flags for higher-risk crypto activity, like those above, the institution should consider crypto-specific enhanced due diligence. This may include requesting additional disclosure from the client about their crypto brokerage or exchange accounts or wallet addresses. The financial institution can then use blockchain analytics to conduct a more detailed assessment on whether there are further higher-risk activities.
View our webinar exploring what recent enforcement actions against banks, fintechs, crypto businesses, and casinos reveal about how illicit actors exploit the financial system and how regulators assess AML/CFT and sanctions compliance programs.










 The Travel Rule Playbook
The Travel Rule PlaybookThis site uses cookies. By continuing to browse the site, you are agreeing to our use of cookies.
Accept settingsHide notification onlySettingsWe may request cookies to be set on your device. We use cookies to let us know when you visit our websites, how you interact with us, to enrich your user experience, and to customize your relationship with our website.
Click on the different category headings to find out more. You can also change some of your preferences. Note that blocking some types of cookies may impact your experience on our websites and the services we are able to offer.
These cookies are strictly necessary to provide you with services available through our website and to use some of its features.
Because these cookies are strictly necessary to deliver the website, refusing them will have impact how our site functions. You always can block or delete cookies by changing your browser settings and force blocking all cookies on this website. But this will always prompt you to accept/refuse cookies when revisiting our site.
We fully respect if you want to refuse cookies but to avoid asking you again and again kindly allow us to store a cookie for that. You are free to opt out any time or opt in for other cookies to get a better experience. If you refuse cookies we will remove all set cookies in our domain.
We provide you with a list of stored cookies on your computer in our domain so you can check what we stored. Due to security reasons we are not able to show or modify cookies from other domains. You can check these in your browser security settings.
These cookies collect information that is used either in aggregate form to help us understand how our website is being used or how effective our marketing campaigns are, or to help us customize our website and application for you in order to enhance your experience.
If you do not want that we track your visit to our site you can disable tracking in your browser here:
We also use different external services like Google Webfonts, Google Maps, and external Video providers. Since these providers may collect personal data like your IP address we allow you to block them here. Please be aware that this might heavily reduce the functionality and appearance of our site. Changes will take effect once you reload the page.
Google Webfont Settings:
Google Map Settings:
Google reCaptcha Settings:
Vimeo and Youtube video embeds:
You can read about our cookies and privacy settings in detail on our Privacy Policy Page.
Privacy Policy